Resource / Online Journal
What is Cyber Warfare? Types and Strategies for Protection
Explore key strategies for protecting against and responding to cyber warfare threats. Stay informed and strengthen your defenses.
Published on Mar 5, 2026

What is Cyber Warfare?
Cyber warfare is the use of cyber operations by one nation-state to attack/target other countries, government systems, and national security. Cyberwarfare attacks are becoming more frequent, and this is one such incident that occurred recently.
The February 28, 2026, Iran cyberattacks were launched alongside joint U.S.–Israel strikes under Operation Roaring Lion / Epic Fury. According to The Jerusalem Post, Israel executed the largest cyberattack in history, collapsing Iran’s internet to 4% connectivity and disabling critical infrastructure, government services, the IRGC, media outlets (IRNA, Tasnim), aviation systems, and regional energy platforms nationwide.
This unprecedented cyber conflict to achieve strategic objectives underscores how nation-state cyber capabilities can destabilize modern economic systems, disable critical systems, and reshape the global cyber domain.
Types of Cyber Warfare Operations and Tactics
Modern cyber warfare tactics blend classic attack vectors with state‑sponsored sophistication. The following breakdown educates readers on types of cyber warfare and then transitions into 2026 AI‑driven evolutions every CISO should anticipate.
Type | Description |
|---|---|
Cyber Espionage | Long‑term infiltration to steal sensitive data, blueprints, and intelligence through implants, backdoors, or supply‑chain compromise. |
DoS / DDoS Attacks | Overwhelm networks with malicious traffic to disable critical systems, causing outages and economic disruption. |
Malware Attacks | Deployment of wipers, trojans, backdoors, or autonomous malware to destroy data, corrupt systems, or conduct long‑term surveillance. |
Ransomware | Encrypts assets for extortion, operational sabotage, or funding state‑aligned threat groups. |
Propaganda / Influence Operations | Digital operations to shift narratives, influence public opinion, or expose embarrassing truths for geopolitical leverage. |
Across these attack types, adversaries exploit legitimate users, identity blind spots, and outdated controls, an evolution of Soviet‑era information disruption now amplified by nation‑states like North Korea and APT groups aligned with Russia, Iran, and the PRC. These operations increasingly target civilian infrastructure, financial systems, and major corporations while bypassing traditional perimeter‑based defenses.
How Does Cyber Warfare Actually Operate?
State actors leverage highly coordinated, layered tactics:
- Initial access via phishing, credential theft, or identity compromise
- Lateral movement through vulnerable computer networks
- Privilege escalation targeting government computer systems and critical operations
- Objective execution: data theft, system destruction, military disruption
Threat actors merge kinetic operations with digital attacks, as seen in the Feb 2026 Iran blackout, creating simultaneous pressure across the cyber domain, military theaters, media ecosystems, and energy networks.
Strategic targeting of core infrastructure, such as
- Electrical power grids
- Aviation & energy systems
- Defense logistics systems
- Private-sector operational tech (OT)
- Citizen‑facing digital services
Psychological & Propaganda Operations: Disinformation, leaks, influence campaigns, and hack-and-leak operations aim to
- Shape public opinion
- Create panic
- Undermine trust in institutions
- Mask or distract from physical or digital military actions
These are the exact tactics used in the Estonian government website attacks and many modern IRGC influence operations.
AI-Driven Attacks
AI has supercharged cyberwarfare operations, enabling attackers to move faster and more autonomously than ever. Adversarial AI now poisons machine‑learning models to fool anomaly‑detection, fraud engines, and IAM systems, letting intruders slip in as legitimate users. At the same time, AI‑generated deepfakes make social engineering far more convincing, powering executive impersonation.
Adding to this, new self‑adapting AI malware can rewrite its own code, steal active sessions, and evade identity‑centric defenses with autonomous C2 shifts, a behavior flagged in 2026 Cloudflare and SentinelOne analyses. In this environment, traditional MFA and perimeter security are no longer enough; organizations need behavioral IAM analytics, continuous verification, session‑integrity monitoring, and autonomous cyber‑defense to survive AI‑accelerated hybrid warfare.
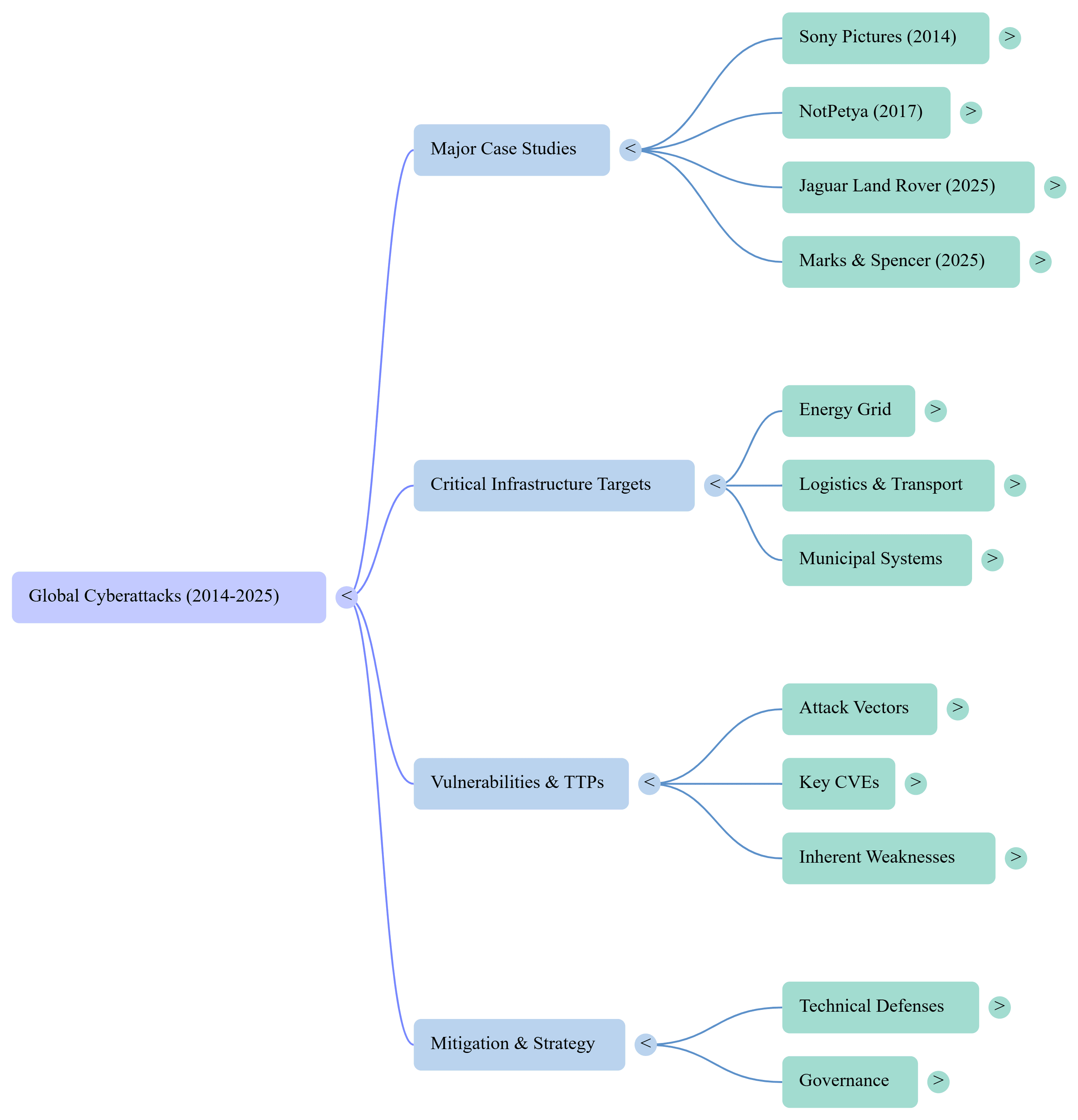
Strategic Case Studies: Lessons from Cyber Operations
Across the past decade, landmark cyber operations, from Russia–Ukraine disruptions to Iran’s nuclear sabotage, North Korea’s Sony breach, Estonia’s digital paralysis, and Iran’s 2026 infrastructure targeting, show a clear pattern: modern cyber warfare is now identity‑centric, infrastructure‑oriented, and geopolitically expressive.
These incidents underscore how nation‑states blend espionage, disruption, and influence into a unified strategy aimed at pressuring economies and eroding institutional trust. For defenders, the lesson is urgent: resilience now depends on identity‑first security, continuous verification, behavioral analytics, and architecting systems that degrade gracefully under nation‑state stress, not on perimeter controls built for a different era.
Risk Framework: Targets and Hybrid Warfare Impacts (200 words)
Disrupting critical infrastructure not only halts operations but also exposes sensitive information, reshaping geopolitical leverage. In modern cyber war, the real battlefield is the convergence point between national capacity and digital dependence.
High‑value targets now extend far beyond classified military systems or government agencies; they encompass the entire economic nervous system: financial exchanges, transportation hubs, healthcare networks, and the power grids that anchor national stability. What makes today’s threat landscape fundamentally different is how adversaries blend digital attacks with the potential for physical damage, turning routine cyber intrusions into catalysts for real‑world disruption. Hybrid warfare blurs these boundaries further, using cyber operations to soften, distract, or distort before traditional maneuvers occur, or to generate strategic leverage without ever crossing into kinetic conflict.
The identity layer remains the most fragile point of failure. Compromised legitimate users, employees, contractors, and third‑party operators offer adversaries the most efficient path into a nation’s computers, major corporations, and cross‑border supply chains. This identity‑driven access enables threat actors to escalate privileges, map critical systems, and pivot across sectors with ease, whether acting on behalf of nation‑states, hacktivist groups, or terrorist organizations.
As hybrid campaigns grow in sophistication, defending infrastructure requires more than hardened networks; it demands adaptive IAM, continuous validation, and architectures capable of withstanding prolonged pressure from well‑resourced adversaries operating across both digital and physical domains.
Future Outlook: Defense Strategies and Scenarios
Looking ahead, effective cyber defense strategies require systemic resilience. National cyber command resilience, where continuous monitoring, rapid containment, and coordinated response are embedded into daily operations. Modern enterprises must treat zero‑trust as an operational mandate, ensuring legitimate users are continuously validated, and every identity, device, and workload is interrogated by design.
Zero‑trust architectures remain the backbone of this evolution, treating every identity, device, and access attempt as untrusted until proven otherwise, ensuring legitimate users are continuously validated across the entire environment. With adversaries accelerating automation, AI‑driven detection becomes indispensable, enabling defenders to flag subtle deviations, correlate weak signals, and adapt in real time.
Enterprises must also prepare for regulatory tightening under frameworks like DORA and NIS2, which elevate expectations for incident readiness, supply chain oversight, and operational durability. Together, these measures define a forward posture centered on integrity, transparency, and adaptability across the cyber domain.
Organizations need partners capable of operationalizing these principles. Top managed security provider TechDemocracy allows businesses to manage identity risk at scale without overtaxing internal staff by integrating security, compliance, and governance into a sustainable operating model that maintains audit readiness.
Recommended articles


24/7 SOC Monitoring: Challenges and Solutions for Continuous Security
Take Your Identity Strategy
to the Next Level
Strengthen your organization's digital identity for a secure and worry-free tomorrow. Kickstart the journey with a complimentary consultation to explore personalized solutions.